Well I guess we all grow old, but this presentation from 2010 is still awesome on using Big Data from R
Category: Internet
Because It is Thursday
Because it is Thursday
I am feeling blue
No one to love me yet
But my reader -you
Game Review: Ingress Calgary versus Ingress Delhi
- I apologize in advance to non gaming readers of this blog.
- I have written about Ingress before here
- I am also experimenting with a new way of writing- in bullet points than in paragraphs.
- Huge number of portals in downtown Calgary compared to Delhi
- Huge number of mind units in Delhi/ India- just made a field with 220 K MUs which is impossible to make or hold in Calgary
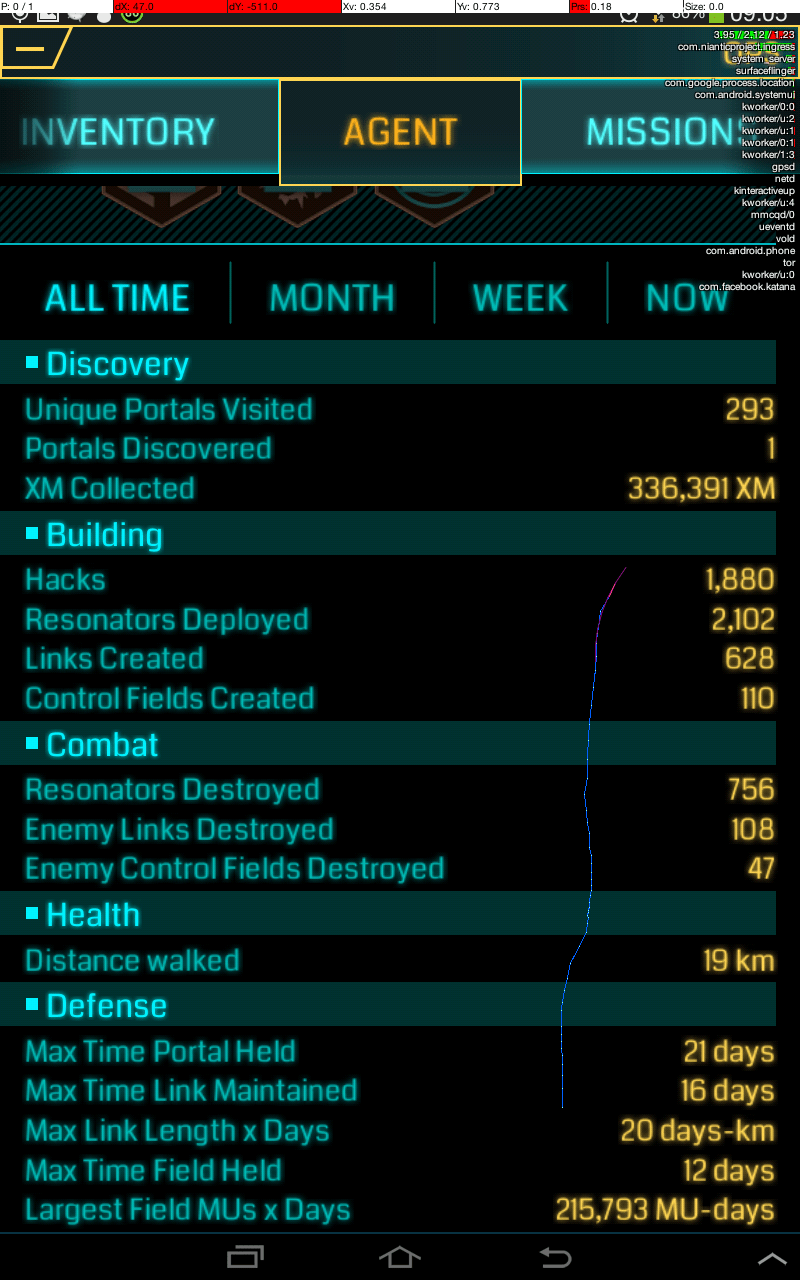
- The smurfs have beaten the frogs in submission in Delhi, with the ability to put up giant 50 million MUs almost at will
- Complete domination in one area leads to boring play for everyone especially for fields that are huge
- Very tough to see the roads etc in a quadruple layer blue field as was the case for last two weeks in Delhi
- Easily the least number of AP I have been scoring since I began playing 5 months ago.
- To my surprise , Ingress keeps rejecting things like Transit stations etc. There seems to be a different strict criterion in different countries in accepting portals. Maybe this is due to bandwidth constraint since Ingress is totally free as to the best of my knowledge.
- I still dont know how Ingress makes money but yeah the geo-game-play data would be awesome for simulations!
- The new stats in Agent tab are good, but maybe some graphs can help
- On a LG phone , Ingress fonts are bloated
- Heaven is a good and cheap data plan on your phone and a great Metro system to transport you to portal glory without wasting much time
- Delhi has a tonne of history. Pity not so many portals!
Cyber Reconnaissance of foreign leaders through implantable medical devices
In an earlier article I had talked of the frightening under preparation of medicine against cyber attacks I had listed some resources- here
Some more papers on this are here https://spqr.eecs.umich.edu/papers/b1kohFINAL2.pdf and here http://www.cis.temple.edu/~jiewu/research/publications/Publication_files/Defending%20Resource%20Depletion%20Attacks%20on.pdf and here http://gao.gov/assets/650/647767.pdf
Sadly there is a complete lack of updated research in public arena. I wonder if the cloud era needs a new eco system of Information Security. Where is John McAffee when you need him?
With Cyber Snooping or Cyber Reconnaissance (NSA) much in the news lately, I wonder if countries monitor the health of foreign leaders like Sonia Gandhi etc through medical devices- a good number of these surgeries are done in the United States for political leaders.
Why does NSA not track child pornography, fake pharma on Internet
I mean how much of the NSA’s budget is spent on combating evils like Merkel’s sms , versus trivial things like baby and child pornographers, people selling fake and illegal drugs and prescription medicine on Internet, and scams like shareware, hostage ware, viruses and simple people downloading illegal intellectual property.
I MEAN HOW MUCH DO THEY SPEND to combat true evil versus assumed security risks like Paris Hilton’s Google Search History or Lady Gaga’s Facebook
If they can build Stuxnet-can they build backdoors that disable wifi on, wifi off signs, or even transmit data for intellectual property theft to give American companies advantages in trade negotiations with the Commies.
hey hey NSA, how many kids do you save from rape today?
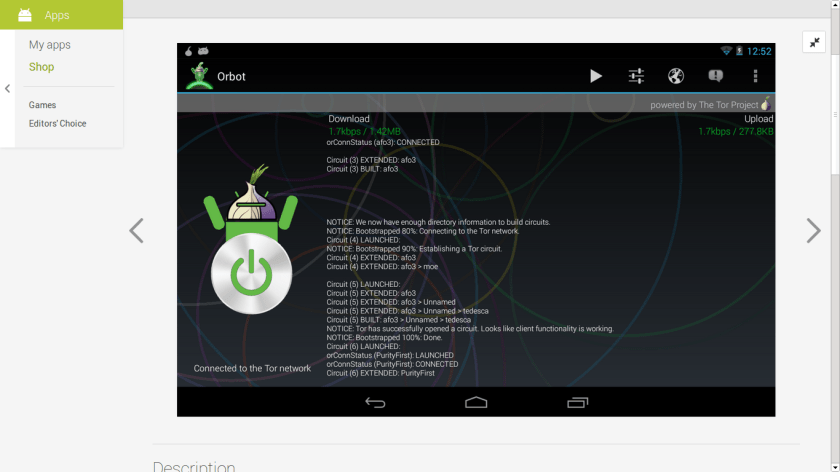
Orbot- going Anonymous on your mobile internet
I really liked the professional design and interface behind Orbot- it is basically Tor for your Android. Add some rooting- and add some crowd sharing love to donate idle bandwidth in your data plan ( or limitation features for usage per period within a certain connection)- and the Tor network can grow even faster.
Also add some pseudo-random interval based auto-switching mechanism rather than wait for user to do it on his own
https://play.google.com/store/apps/details?id=org.torproject.android
Description
Data Privacy and OECD
I really liked revisiting these privacy principles at http://oecdprivacy.org/
I wonder if the internet uses them??
The OECD Privacy Principles are part of the OECD Guidelines on the Protection of Privacy and Transborder Flows of Personal Data, which was developed in the late 1970s and adopted in 1980.
1. Collection Limitation Principle
There should be limits to the collection of personal data and any such data should be obtained by lawful and fair means and, where appropriate, with the knowledge or consent of the data subject.
2. Data Quality Principle
Personal data should be relevant to the purposes for which they are to be used, and, to the extent necessary for those purposes, should be accurate, complete and kept up-to-date.
3. Purpose Specification Principle
The purposes for which personal data are collected should be specified not later than at the time of data collection and the subsequent use limited to the fulfilment of those purposes or such others as are not incompatible with those purposes and as are specified on each occasion of change of purpose.
4. Use Limitation Principle
Personal data should not be disclosed, made available or otherwise used for purposes other than those specified in accordance with Paragraph 9 except:
a) with the consent of the data subject; or
b) by the authority of law.
5. Security Safeguards Principle
Personal data should be protected by reasonable security safeguards against such risks as loss or unauthorised access, destruction, use, modification or disclosure of data.
6. Openness Principle
There should be a general policy of openness about developments, practices and policies with respect to personal data. Means should be readily available of establishing the existence and nature of personal data, and the main purposes of their use, as well as the identity and usual residence of the data controller.
7. Individual Participation Principle
An individual should have the right:
a) to obtain from a data controller, or otherwise, confirmation of whether or not the data controller has data relating to him;
b) to have communicated to him, data relating to him
i) within a reasonable time;
ii) at a charge, if any, that is not excessive;
iii) in a reasonable manner; and
iv) in a form that is readily intelligible to him;c) to be given reasons if a request made under subparagraphs (a) and (b) is denied, and to be able to challenge such denial; and
d) to challenge data relating to him and, if the challenge is successful to have the data erased, rectified, completed or amended.
8. Accountability Principle
A data controller should be accountable for complying with measures which give effect to the principles stated above.
News
- 2010 is the 30th anniversary of the Guidelines on the Protection of Privacy and Transborder Flows of Personal Data
- OECD is preparing an anniversary report on the evolving privacy landscape
- There will be a review of the Guidelines beginning in 2011, per the Ministers in the Seoul Declaration for the Future of the Internet Economy.
Other Privacy Frameworks
APEC Privacy Framework
The Asia-Pacific Economic Cooperation (APEC) Privacy Framework overlaps with other frameworks; however, it concentrates on actual or potential harm as a result of disclosing information, rather than individuals’ rights pertaining to their information
The Internet Economy on the Rise:
Progress since the Seoul Declaration
Published in September 2013, this book reviews progress made since the 2008 OECD Seoul Declaration for the Future of the Internet Economy and identifies areas for future work.
Overall, the review shows that the Internet economy has become a new source of growth, with the potential to boost the whole economy, to foster innovation, competitiveness and user participation, and to contribute effectively to the prosperity of society as a whole.
The OECD Policy Guidance for Protecting and Empowering Consumers in Communication Services (Annex B) addresses some of the key issues currently facing consumers in this market.
The guidance advocates:
Informing consumers about potential security and privacy risks in using communication services and available measures to limit these risks.
The OECD Policy Guidance on Radio Frequency Identification (Annex C) encourages research on the economic and social impacts of such technologies The guidance points out the need to prevent and mitigate security risks and to address privacy concerns arising when information relating to an identified or identifiable individual is collected or processed. 
AJAY- So the guidelines are there. But who all are following them and who aren’t?
Revised Principles-
http://www.oecd.org/sti/ieconomy/2013-oecd-privacy-guidelines.pdf