In my previous post in the hacker series https://decisionstats.com/2013/03/20/hacking-for-beginners-top-website-hacks/ , we noted that SQL Injection remains a top method for security vulnerabilities. Accordingly- here is a list of resources to learn SQL Injection
Definition
SQL injection is a code injection technique that exploits a security vulnerability in an application’s software. The vulnerability happens when user input is either incorrectly filtered for string literal escape characters embedded in SQL statements or user input is not strongly typed and unexpectedly executed. SQL injection is mostly known as an attack vector for websites but can be used to attack any type of SQL database.
Basic Tools
- SQL Inject Me
https://addons.mozilla.org/en-us/firefox/addon/sql-inject-me/
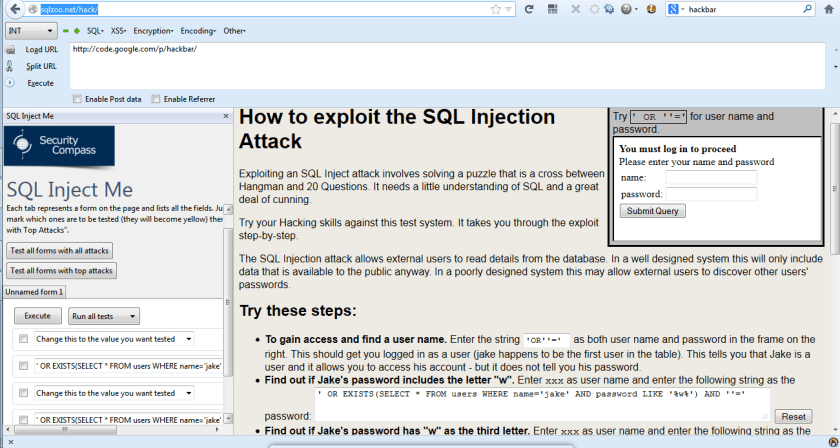
SQL Inject Me is the Exploit-Me tool used to test for SQL Injection vulnerabilities.
The tool works by submitting your HTML forms and substituting the form value with strings that are representative of an SQL Injection attack.The tool works by sending database escape strings through the form fields. It then looks for database error messages that are output into the rendered HTML of the page.
The tool does not attempting to compromise the security of the given system. It looks for possible entry points for an attack against the system. There is no port scanning, packet sniffing, password hacking or firewall attacks done by the tool.
- Hackbar
https://addons.mozilla.org/en-US/firefox/addon/hackbar/
and http://code.google.com/p/hackbar/
This toolbar will help you in testing sql injections, XSS holes and site security. It is NOT a tool for executing standard exploits and it will NOT teach you how to hack a site
- SQLMap
sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers.
Basic Tutorials ( in order of learning)
A site for testing SQL Injection attacks. It is a test system and can be used for honing your SQL Skills.
Intermediate Tutorials on End to End SQL Injection
Step 1: Finding Vulnerable Website:
Step 2: Checking the Vulnerability:
To check the vulnerability , add the single quotes(‘) at the end of the url and hit enter.
If you got an error message , then it means that the site is vulnerable
Step 3: Finding Number of columns:
Step 4: Find the Vulnerable columns:
Step 5: Finding version,database,user
Step 6: Finding the Table Name
Step 8: Finding the Admin Panel:
from http://www.breakthesecurity.com/2010/12/hacking-website-using-sql-injection.html
- Next Tutorial uses an automated tool called Havij from
http://www.itsecteam.com/products/havij-v116-advanced-sql-injection/
and the tutorial is at
http://cybersucks.blogspot.in/2013/01/hacking-website-using-sql-injectionfull.html